GenCyber
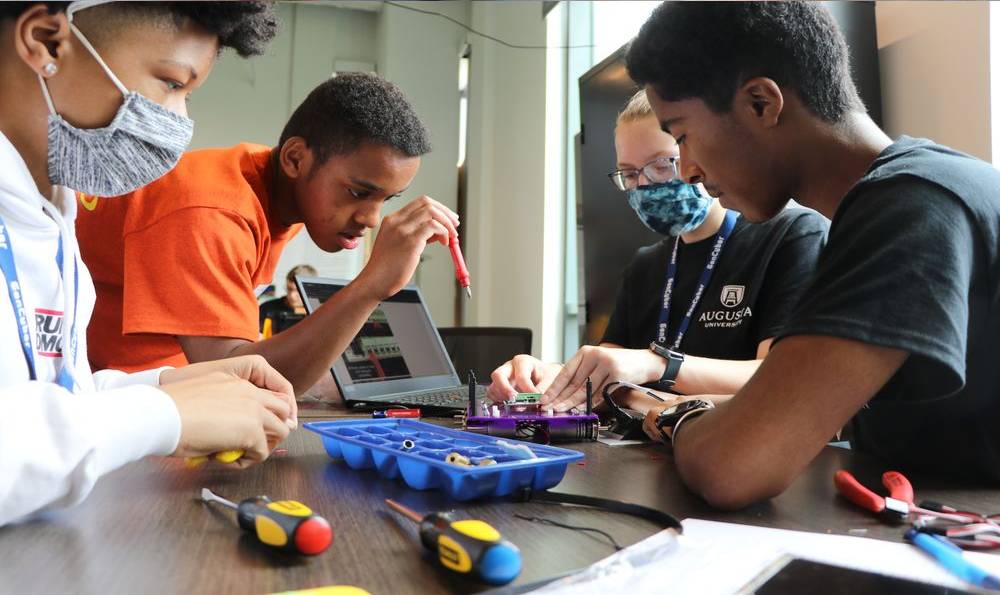
Inspiring the next generation of cybersecurity professionals
Sponsored by the National Security Agency and National Science Foundation, GenCyber is a 6-day, residential summer camp open to students of diverse cybersecurity experience. If accepted to the yearly camp cohort, campers will enjoy engaging, hands-on learning opportunities including classroom activities and field trips to NSA Georgia and the Fort Eisenhower Cyber Center of Excellence.
GenCyber Updates
Thank you for your participation last year! We’re taking a hiatus this year and will not be hosting a camp for the summer. Stay tuned for updates and important announcements.

Goals of the GenCyber Camp:
- Expose high school students to potential careers and issues in cybersecurity.
- Teach students to secure their digital lifestyle.
- Demonstrate to students why "Internet of Things" devices need to be secured.
- Augusta University's program is designed to teach the GenCyber First Principles (listed below), cybersecurity ethics and online safety and hygiene.
Subjects covered in GenCyber include:
GenCyber Cybersecurity Concepts: Defense in Depth, Confidentiality, Integrity, Availability, Thinking like an Adversary, and Keeping it Simple
In addition to these cybersecurity concepts, Augusta University's GenCyber program will also cover:
- Cryptography
- Cryptanalysis
- Robotics
- Python programming





Contact Us
GenCyber Camp at Augusta University
706-721-1110
School of Computer and Cyber Sciences
Facebook Group: GenCyber Camp
GenCyber FAQ's
When is GenCyber?
Who is eligible to attend GenCyber?
Rising high school juniors and seniors are eligible to attend GenCyber--- completely free of charge!
Are there specific criteria needed for acceptance into GenCyber?
Students shall demonstrate exceptional skill, creativity and knowledge in math and science. Academic achievement and social maturity are considered in the selection process. There is no specific numerical minimum test score or GPA set by the committee, however, admittance to the program is competitive.
Will I be graded or given credit for work completed at GenCyber?
The GenCyber camps are prestigious, pre-collegiate summer programs, but they do not provide grades or college course credit. Accepted students are not required to take any exit exams or standardized tests regarding major courses of study.
I am a special needs student and require special accommodations to attend GenCyber. Can I still participate if accepted?
GenCyber First Principles
Abstraction
A fancy word for summarizing or explaining in a way that is easily understood.
Modularity
Able to be inserted or removed from a project, each module has its own function interchangeable with other modules.
Domain Separation
Separating areas where resources are located prevents accidents and loss of data, keeping information worlds from colliding.
Resource Encapsulation
Resources hardware, system objects, or processes must be separated and used as intended.
Information Hiding
Information hiding is any attempt to prevent people from being able to see information. It can be hiding the content of a letter, or it can be applied to hiding how the letter is delivered.
Process Isolation
A process occurs when a task is executed. Keeping processes separate prevents the failure of one process from negatively impacting another.
Layering
Cyber security uses multiple layers of defenses for protecting information. If one layer is defeated, then the next one should catch it.
Simplicity of Design
The less complicated something is, the less likely it is to have problems. It is also easier to fix and troubleshoot.
Least Privilege
One of the ways to protect information is by limiting what people can do with your information and resources. You may allow someone to read a letter, but not edit it.
Minimization
Minimization refers to having the least functionality of a program or device. The goal is to simplify and decrease the number of ways the software can be exploited.